Regression #14877
closedImport PKCS #12 (PFX) certificate error when using legacy/low ciphers
100%
Description
Tested against:
23.09-BETA (amd64) built on Fri Oct 13 6:00:00 UTC 2023 FreeBSD 14.0-CURRENT
When trying to import a PKCS #12 certificate, I am getting the following error:
The following input errors were detected: * The submitted password does not unlock the submitted PKCS #12 certificate.
I can successfully import the same cert using the same password in the 23.05.1.
I generated the certificate on macOS Keychain Access.
Keychain Access --> Certificate Assistant --> Create a certificate.
Files
 Updated by Lev Prokofev over 2 years ago
Updated by Lev Prokofev over 2 years ago
Tested, on
23.09-BETA (amd64)
built on Fri Oct 13 6:00:00 UTC 2023
FreeBSD 14.0-CURRENT
It works fine with a Cert generated on a Win server using AES256-SH256 or 3DES-SHA1
 Updated by Danilo Zrenjanin over 2 years ago
Updated by Danilo Zrenjanin over 2 years ago
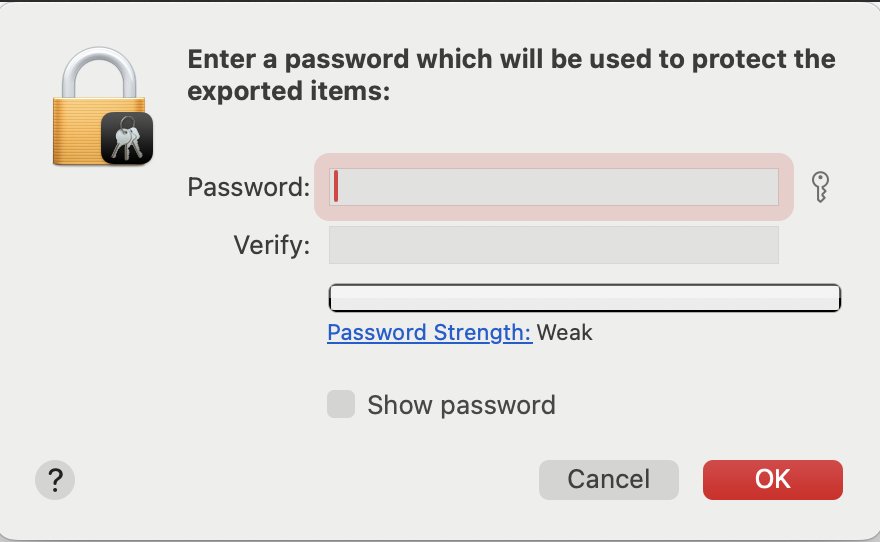
In the MacOS, the password gets generated once you right-click on the cert in the Keychain Access and choose export.
After entering that password in the pfSense import certificate page, it fails with the error message:
The following input errors were detected: * The submitted password does not unlock the submitted PKCS #12 certificate.
The same procedure works fine in 23.05.1.
 Updated by Jim Pingle over 2 years ago
Updated by Jim Pingle over 2 years ago
- Subject changed from Import PKCS #12 (PFX) certificate error to Import PKCS #12 (PFX) certificate error when using legacy/low ciphers
- Status changed from New to In Progress
- Assignee set to Jim Pingle
- Target version set to 2.8.0
- Plus Target Version set to 23.09
That's because when it gets exported it's using a low/old/deprecated cipher set. Then the import code doesn't support those.
The only way I can see to fix it is to enable the legacy provider by default in OpenSSL which we may need to do for this release. Otherwise we'd have to completely rewrite PKCS#12 import to use the openssl CLI commands or we'd have to tell users we can't import these bundles.
For safety/compatibility at least in this release, enabling the legacy provider should be OK.
 Updated by Jim Pingle over 2 years ago
Updated by Jim Pingle over 2 years ago
- Release Notes changed from Default to Force Exclusion
 Updated by Jim Pingle over 2 years ago
Updated by Jim Pingle over 2 years ago
- Status changed from In Progress to Feedback
- % Done changed from 0 to 100
Fixed by commit:275ae19ad70336f06ed53d655ceb96c8b2ab56f0 which enables the legacy provider by default.
If testing via applying a patch instead of by snapshot upgrade, either restart PHP-FPM and nginx (e.g 16/11 from the menu) or reboot after applying the patch.
 Updated by Jim Pingle over 2 years ago
Updated by Jim Pingle over 2 years ago
After internal discussion we decided not to enable the legacy provider by default because it had other potentially negative repercussions.
I reverted that change and I have imported a new change to the error message that notes that if it fails it may be due to a bad cipher.
In other words, these P12 files will fail but that's expected and not a bug, and that failure case should be made more obvious by the updated error message.
 Updated by Danilo Zrenjanin over 2 years ago
Updated by Danilo Zrenjanin over 2 years ago
- Status changed from Feedback to Resolved
Tested against the latest Beta release.
The error message now accurately describes the cause of the failure.
The following input errors were detected: The submitted password does not unlock the submitted PKCS #12 certificate or the bundle uses unsupported encryption ciphers.
I am marking this ticket resolved.
 Updated by Jim Pingle over 2 years ago
Updated by Jim Pingle over 2 years ago
- Target version changed from 2.8.0 to 2.7.1